Stalled SaaS deals don't just delay software rollouts. They create hidden costs: wasted stakeholder time, missed productivity gains, and vendor relationships that sour before contracts are signed. For mid-sized companies with 500 or more employees, security reviews derail the majority of enterprise procurement cycles, often because buyers arrive unprepared. This article walks you through a structured, repeatable workflow that addresses every stage, from the initial build-vs-buy decision through security artifact readiness, execution, and verification, so your team can move from evaluation to signed contract with confidence.
Table of Contents
- Understand the SaaS decision-making framework
- Preparation: Security review and procurement prerequisites
- Execution: Step-by-step SaaS decision process
- Verification: Common pitfalls and troubleshooting tips
- What most SaaS buyers miss about workflow and security review
- Take your SaaS decision-making workflow further with SaaSpare
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Framework clarity | Applying structured decision frameworks prevents confusion and supports scalable SaaS purchases. |
| Security review speed | Having SOC 2 artifacts ready is crucial to avoid procurement delays and winning stakeholder trust. |
| Hybrid solutions | Most SaaS workflows benefit from flexible build, buy, or bolt-on combinations for performance and integration. |
| Cycle-time reduction | Pre-planning security reviews and artifacts can shave weeks off your SaaS buying process. |
| Actionable verification | Regular troubleshooting ensures your workflow delivers faster, stress-free decision outcomes. |
Understand the SaaS decision-making framework
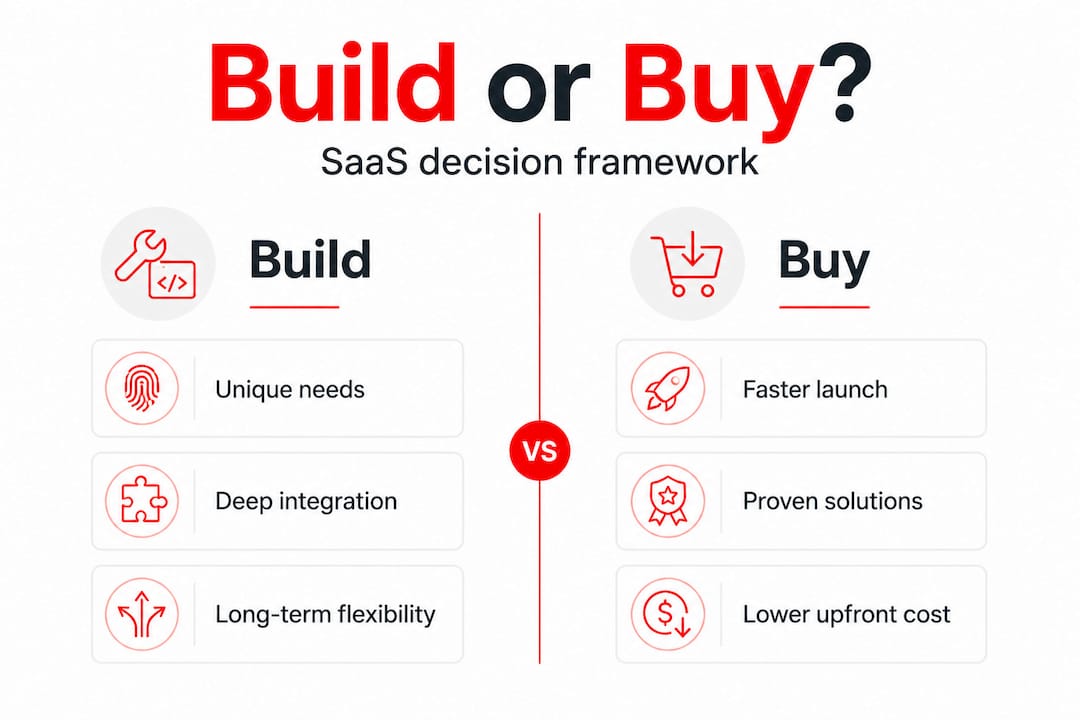
Every SaaS purchase starts with a deceptively simple question: should we build it, buy it, or bolt something on to what we already have? The answer shapes your budget, your timeline, and the long-term flexibility of your tech stack. Getting it wrong early means expensive course corrections later.
Experts recommend a decision framework using five tests: differentiation, process volatility, integration depth, five-year cost, and capability to maintain. When answers are mixed across those five tests, a hybrid or bolt-on approach is often the most practical outcome. Understanding where each test points your organization is the first real step in a structured workflow.
Here is what each test actually means in practice:
- Differentiation: Does this capability give your company a competitive edge? If yes, building may be worth the investment. If it is a commodity function like expense tracking or email, buy.
- Process volatility: How frequently does this process change? High-change processes favor SaaS because vendors absorb update costs. Low-change, stable processes may justify a custom build.
- Integration depth: How deeply does this tool need to connect with your existing systems? Deep, custom integrations often tip the scales toward building or using a bolt-on layer.
- Five-year cost: Total cost of ownership over five years, including maintenance, upgrades, and staffing, often reveals that SaaS is cheaper than it appears upfront, especially for smaller teams.
- Capability to maintain: Does your team have the engineering bandwidth to own a custom solution long-term? If not, buying is almost always the safer bet.
The following table summarizes how each test maps to a likely outcome:
| Framework test | Points toward build | Points toward buy | Points toward hybrid |
|---|---|---|---|
| Differentiation | High differentiation | Commodity function | Partial differentiation |
| Process volatility | Stable, low change | High change | Mixed change patterns |
| Integration depth | Minimal integration needed | Standard API integrations | Deep and custom integrations |
| Five-year cost | Low total cost of ownership | High build and maintain cost | Cost varies by component |
| Capability to maintain | Strong internal engineering | Limited internal resources | Partial internal capability |
When you run these tests with your stakeholders and find that two or three tests point in different directions, that is a reliable signal to explore hybrid options. You can explore SaaSpare's SaaS comparison library to see how tools in specific categories stack up across these criteria, which saves significant research time during the framework stage.
It is also worth noting that the framework should be revisited every 12 to 18 months. Business priorities shift. A tool that was worth building two years ago may now have a SaaS alternative that covers 90% of your requirements at a fraction of the ongoing cost. Applying the comparison methodology consistently, rather than relying on gut instinct, keeps decisions grounded in current data rather than legacy assumptions.
Preparation: Security review and procurement prerequisites
Understanding the framework is step one. The next challenge is preparing for the procurement obstacles that derail even well-structured decisions. Security review is the most common culprit.
Security review is unavoidable in enterprise SaaS procurement. Many deals stall without a SOC 2 report, and the review typically requires a current SOC 2 report, a completed security questionnaire, and a named security contact with a defined SLA. For organizations with 500 or more employees, this applies to 85 to 95 percent of software purchases. That is not an edge case. It is the standard.

The problem is that most buyers treat security review as something that happens after they have selected a vendor. By that point, you are already deep in the procurement cycle, stakeholders are aligned, and a missing artifact can add weeks or even months to your timeline. The smarter approach is to treat security readiness as a prerequisite, not a final step.
Here is a numbered checklist of the security artifacts you should gather before initiating formal procurement:
- Current SOC 2 Type 1 or Type 2 report from the vendor, ideally issued within the last 12 months.
- Completed security questionnaire, using your organization's standard template or the vendor's pre-filled version.
- Named security contact at the vendor, with a documented response SLA for security incidents.
- Data processing agreement (DPA) or equivalent privacy documentation, especially if you handle personal data.
- Penetration testing summary, particularly for tools that will access sensitive internal systems.
- Business continuity and disaster recovery documentation, confirming uptime commitments and recovery time objectives.
"Plan SOC readiness before procurement triggers it. Otherwise, security review can add substantial cycle time to an already complex process." — SOC readiness advice
The following table shows typical procurement timelines with and without security artifact readiness:
| Scenario | Estimated procurement time | Key risk |
|---|---|---|
| All artifacts ready at kickoff | 3 to 6 weeks | Minimal delays |
| SOC 2 report missing at kickoff | 8 to 14 weeks | Vendor audit backlog |
| Security questionnaire incomplete | 6 to 10 weeks | Back-and-forth review cycles |
| No named security contact | 5 to 9 weeks | Escalation delays |
Pro Tip: Use SaaSpare's deal radar to track vendor security certifications and flag which tools already have SOC 2 documentation publicly available. This cuts your artifact collection time significantly before you even reach out to a vendor.
Reviewing security review timing across different vendor categories also helps you anticipate which tools are likely to require the most intensive review, so you can allocate internal resources accordingly.
Execution: Step-by-step SaaS decision process
Once your prerequisites are clear, here is how to execute your workflow efficiently. The goal is to move through each stage without creating bottlenecks or requiring rework.
-
Run the five-test framework with your full stakeholder group. Do not let this be a solo exercise. Product managers, finance officers, and IT security leads often score the same test differently, and those differences surface important assumptions early.
-
Document your framework scores and the rationale behind each one. A simple scoring matrix works well here. When stakeholders disagree, the documentation becomes the basis for a structured conversation rather than a political debate.
-
Shortlist vendors based on framework outcomes. If you are buying, use category-specific comparison data. If you are building or using a hybrid, define the scope of the custom component clearly before evaluating bolt-on options.
-
Assess SOC 2 requirements based on your risk tolerance. SOC 2 Type 1 vs Type 2 maps directly to procurement timing and risk tolerance. Type 1 proves that controls exist at a point in time. Type 2 proves those controls have been operating effectively over an observation period, typically six to twelve months. For tools handling sensitive financial or HR data, Type 2 is almost always required.
-
Request and review security artifacts in parallel with commercial negotiation. Do not wait for the contract redline process to start security review. Running them in parallel can cut two to four weeks from your total cycle time.
-
Finalize hybrid architecture if applicable. If your framework tests pointed toward a hybrid, define the integration layer clearly before signing. Ambiguous integration scope is one of the most common sources of post-contract disputes.
-
Complete internal approval routing with all artifacts attached. Finance, legal, and security approvals go faster when the documentation package is complete at submission.
Pro Tip: Review the comparison methodology to understand how to weight vendor scoring criteria before you start shortlisting. Consistent scoring criteria prevent the common problem of comparing tools on different dimensions across different stakeholders.
For teams evaluating security tools specifically, checking a security artifact comparison between leading vendors gives you a concrete benchmark for what a well-prepared vendor security package looks like.
Verification: Common pitfalls and troubleshooting tips
Having completed the workflow steps, the final stage is making sure your process does not stall at the finish line. Several predictable pitfalls trip up even experienced procurement teams.
The most common pitfalls include:
- Unclear requirements at the start. Vague requirements lead to vendor shortlists that are too broad, scoring debates that drag on, and stakeholder misalignment that resurfaces during contract review.
- Missing or outdated security artifacts. A SOC 2 report issued 18 months ago may not satisfy your security team's requirements. Always confirm the issuance date before submitting for internal review.
- Integration gaps discovered late. Teams often assume standard API integrations will work without validating them against their specific tech stack. This surfaces as a blocker during implementation, not procurement, which is even more costly to fix.
- Undefined hybrid scope. When a hybrid solution is chosen, the boundary between the SaaS component and the custom component is often left ambiguous. This creates budget overruns and timeline slippage.
- Single-threaded vendor relationships. Relying on one contact at the vendor for both commercial and security questions slows everything down. Establish separate contacts for each workstream early.
"Plan SOC readiness before procurement triggers it; otherwise security review adds substantial cycle time."
Pro Tip: Before moving any vendor to the procurement stage, confirm that all required security artifacts are not just collected but reviewed and approved by your internal security team. Submitting incomplete packages to procurement is one of the most avoidable sources of delay.
Tracking security review timing across your vendor shortlist helps you anticipate which reviews will take longer and sequence your procurement accordingly. Similarly, using SaaSpare's deal radar to monitor vendor pricing changes and contract terms helps you avoid last-minute surprises that can derail final approval.
One additional verification step that teams often skip: confirm that the SaaS tool you selected still matches your original framework scores after the negotiation process. Scope changes during commercial negotiation sometimes shift the integration depth or cost profile enough to warrant revisiting the build-vs-buy decision before signing.
What most SaaS buyers miss about workflow and security review
Here is the uncomfortable reality: most SaaS buyer guides treat security review as a checkbox. Pass the review, move on. But the security review stage is actually one of the most revealing moments in any vendor relationship.
How a vendor handles your security questionnaire tells you a great deal about how they will handle a data incident, a support escalation, or a contract dispute. Vendors who respond quickly, with complete documentation and a named security contact, are demonstrating operational maturity. Vendors who delay, deflect, or send generic responses are showing you exactly how they will behave when something goes wrong post-contract.
Pre-emptive artifact collection does more than cut weeks from your cycle time. It changes the power dynamic in the negotiation. When you arrive at the commercial stage with security review already complete, you are negotiating from a position of readiness rather than urgency. Urgency is expensive. It leads to worse pricing, shorter contract terms, and less favorable SLAs.
Rigid decision trees also fail in practice. The build-vs-buy-vs-bolt-on framework is most valuable when it is treated as a living tool, not a one-time exercise. Organizations that revisit their framework scores as vendor landscapes evolve consistently make better long-term decisions than those that lock in a choice and defend it regardless of new information.
The teams that consistently get SaaS procurement right are the ones who treat the workflow as a repeatable system, not a project. They invest in making unbiased decisions by using consistent criteria, transparent data, and structured review processes. That investment pays off in shorter cycle times, better vendor relationships, and software that actually gets used.
Take your SaaS decision-making workflow further with SaaSpare
If you are ready to put a structured workflow into practice, SaaSpare gives you the tools to do it with confidence. The platform provides unbiased, data-driven comparisons across 16 SaaS verticals, with pricing extracted directly from vendor sites and updated automatically.

You can browse the full SaaS comparison library to shortlist tools by category, budget, and feature requirements without wading through sponsored reviews or vendor-influenced rankings. Every comparison follows a consistent comparison methodology that surfaces hidden fees, per-seat charges, and integration requirements so you can apply your framework tests with real data. Whether you are evaluating your first enterprise SaaS purchase or optimizing a stack of 30 tools, SaaSpare is built to support every stage of the decision-making workflow.
Frequently asked questions
What is the most common cause of delays in SaaS procurement?
Incomplete security review, especially missing SOC 2 reports and questionnaires, causes the majority of enterprise procurement delays. Arriving at the security review stage without complete artifacts forces teams into extended back-and-forth cycles with vendors.
How does SOC 2 Type 1 differ from Type 2 in SaaS buying?
Type 1 proves controls exist at a specific point in time, while Type 2 proves those controls have been operating effectively over an extended observation period, typically reducing buyer risk for sensitive data environments.
Which tests should be included in a SaaS build vs buy vs bolt-on framework?
The five key tests are differentiation, process volatility, integration depth, five-year cost, and capability to maintain the solution. Mixed results across these tests typically point toward a hybrid approach.
What should buyers prepare before starting a SaaS procurement?
Buyers should have completed security questionnaires, updated SOC 2 reports, and a named security contact with defined SLAs ready before initiating formal procurement to avoid timeline delays.
